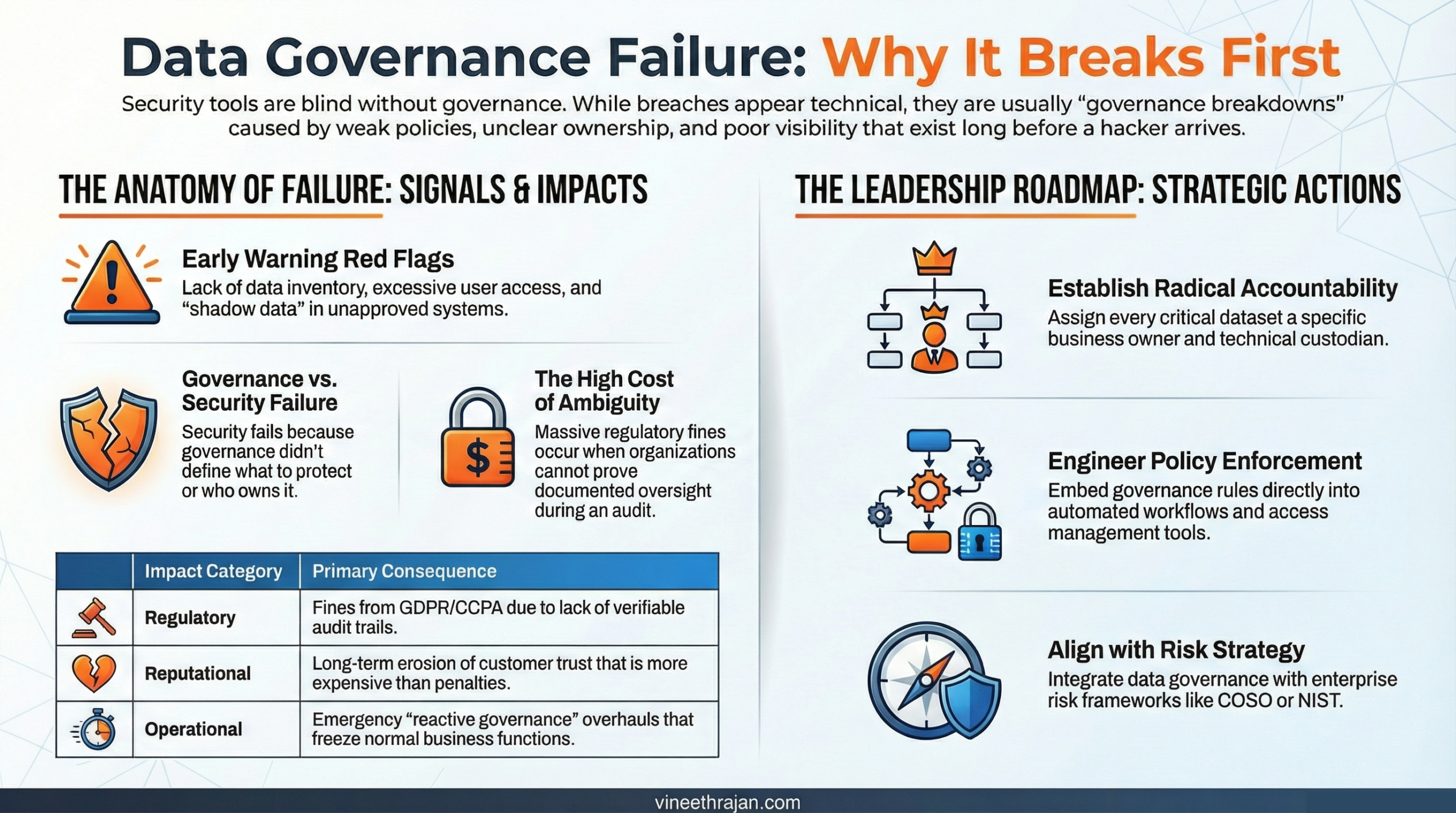
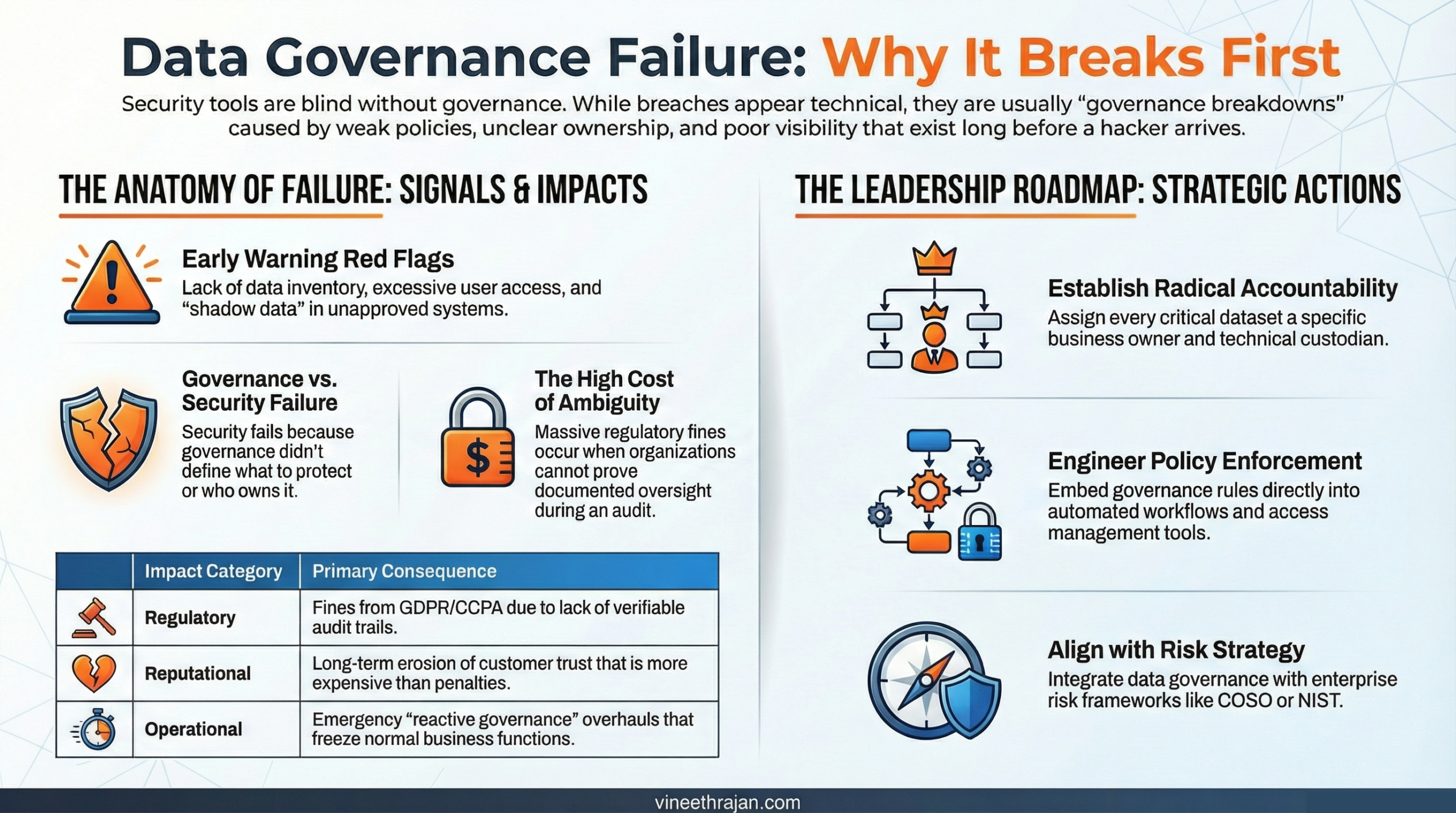
Security does not set its own priorities in isolation; it depends on governance frameworks to define what matters most. Governance determines which datasets require encryption, which systems demand multi-factor authentication, what regulatory obligations apply, and how incident response efforts should be prioritized when an event occurs. These decisions are not purely technical. They are rooted in risk tolerance, data classification, legal exposure, and business impact. When governance is weak or undefined, security teams are forced to operate without clear direction, protecting everything equally or, worse, protecting the wrong things. In that environment, security is not strategic, it is blind.
Another major cause of data governance failure is unclear accountability. When no one formally “owns” the data, oversight quickly erodes. Access reviews are skipped because they are assumed to be someone else’s responsibility. Risk assessments remain incomplete or outdated. Data quality issues multiply without a clear steward to resolve them. Compliance reporting becomes inconsistent, fragmented across departments, and difficult to defend under regulatory scrutiny.
By the time a breach occurs, leadership often discovers that responsibility was diffused across IT, legal, compliance, and business units with no single accountable owner. In that vacuum, governance does not fail suddenly. It fails gradually, until the consequences become impossible to ignore.
The Real Cost of Data Governance Failure
The damage from a breach extends far beyond technical containment and remediation. While security teams focus on patching systems and closing vulnerabilities, the deeper and more enduring consequences often stem from governance breakdowns.
1. Regulatory Penalties
Without well-documented governance controls, demonstrating compliance becomes a challenge at the worst possible moment. Regulators expect clear audit trails, up-to-date policy documentation, formal risk assessments, and verifiable access logs. Frameworks such as General Data Protection Regulation and California Consumer Privacy Act place accountability squarely on organizations to prove responsible data stewardship. When governance records are incomplete, inconsistent, or missing altogether, fines and enforcement actions escalate. Not just because a breach occurred, but because oversight cannot be demonstrated.
2. Reputational Erosion
Customers and partners rarely distinguish between governance failure and security failure. To them, exposure of sensitive data signals a breakdown of trust. Once confidence is shaken, rebuilding credibility can take years and in highly competitive markets, some organizations never fully recover. Trust, once lost, becomes far more expensive to restore than any regulatory penalty.
3. Operational Disruption
Post-breach investigations frequently uncover deeper governance chaos beneath the surface. In response, organizations may be forced to halt certain operations, freeze data systems, conduct emergency audits, and retroactively classify or reclassify sensitive datasets. This reactive governance overhaul diverts executive attention, strains internal resources, and disrupts normal business functions.
In the end, the most expensive part of a breach is often not the technical fix, it is the organizational reckoning that follows.
How to Prevent Data Governance Failure After a Breach
A breach can become a turning point but only if leadership treats it as a governance reset, not just a security incident. Recovery is not only about patching systems. It is about correcting the structural weaknesses that allowed the exposure to occur in the first place.
Step 1: Establish Clear Data Ownership
Every critical dataset must have a clearly identified business owner, a technical custodian, and defined accountability metrics tied to performance and oversight. Ownership is what transforms policies from passive documents into enforceable standards. When responsibility is explicit, access reviews happen, risk assessments are maintained, and compliance obligations are actively monitored. Ownership drives enforcement.
Step 2: Build a Data Inventory
You cannot govern what you cannot see. A centralized, continuously updated data inventory or catalog should document data location, sensitivity classification, retention requirements, and access permissions. This visibility provides the foundation for risk prioritization and regulatory defense. When data flows are mapped and understood, blind spots shrink significantly.
Step 3: Implement Policy Enforcement Mechanisms
Policies must move beyond documentation and into operational systems. Governance rules should be embedded directly into access management platforms, data lifecycle management tools, monitoring dashboards, and compliance reporting frameworks. Automation ensures consistency, reduces human error, and creates defensible audit trails. Governance must be engineered into workflows, not left to manual interpretation.
Step 4: Align Governance With Risk Strategy
Data governance should connect directly to enterprise risk management frameworks such as Committee of Sponsoring Organizations of the Treadway Commission (COSO) or National Institute of Standards and Technology (NIST). High-risk data assets require stronger access controls, continuous monitoring, and executive-level oversight. By aligning governance decisions with risk tolerance and business impact, organizations shift from reactive compliance to proactive resilience.
When governance is embedded into ownership, visibility, enforcement, and risk alignment, a breach becomes not just a lesson learned but a catalyst for lasting structural improvement.
Rebuilding Trust Through Governance Maturity
Recovering from data governance failure requires more than technical fixes. It demands cultural change. Trust is rebuilt not through statements, but through structural reform. Organizations must shift from siloed data management to true enterprise-wide oversight, from reactive security measures to preventive governance disciplines, and from a compliance-only mindset to value-driven governance that treats data as both an asset and a responsibility.
This transformation depends on visible executive sponsorship, empowered cross-functional governance committees, and clearly defined, measurable KPIs that track ownership, risk reduction, policy adherence, and data quality. Governance cannot sit solely within IT or compliance; it must operate as a coordinated business function.
Governance maturity does not happen overnight. It evolves through consistent, incremental progress, quarterly audits that verify controls, structured policy refresh cycles that reflect regulatory and business changes, automated data classification that reduces manual gaps, and continuous monitoring that reinforces accountability. Over time, these steady improvements rebuild resilience, restore stakeholder confidence, and transform governance from a reactive necessity into a strategic strength.
Practical Strategies to Strengthen Governance Today
Strengthening governance does not require a multi-year transformation plan to begin making progress. There are practical, high-impact actions organizations can implement immediately to reduce risk and reinforce accountability.
Start by conducting a formal governance gap assessment to identify weaknesses in ownership, classification, retention, and oversight controls. Review privileged access across critical systems to ensure least-privilege principles are enforced and regularly validated. Launch structured quarterly data ownership reviews so business owners actively confirm accountability for their datasets. Integrate governance metrics such as access review completion rates, policy exceptions, and data classification coverage into board-level reporting to elevate visibility and executive accountability. Finally, train employees across all departments on their data handling responsibilities, reinforcing that governance is not just an IT concern but an organizational obligation.
Small, consistent improvements compound over time. When governance becomes part of routine operational discipline rather than a reactive response, the likelihood of another data governance failure drops significantly.
Common Mistakes Organizations Make
Even after experiencing a breach, some organizations fall back into the same patterns that created governance weaknesses in the first place. Recovery efforts stall when governance is treated as an IT-only initiative rather than an enterprise responsibility owned by business leadership. Policies are rewritten and circulated, but without embedded enforcement mechanisms, they remain theoretical rather than operational.
Another common mistake is failing to monitor policy adherence consistently. Governance cannot rely on assumptions; it requires measurable oversight and regular validation. Meanwhile, shadow IT and unmanaged data environments continue to grow unchecked, creating blind spots that undermine formal controls. Perhaps most underestimated of all is cultural resistance, the reluctance to change processes, accept accountability, or prioritize governance amid competing business pressures.
Avoiding these pitfalls is essential. Sustainable recovery depends not just on stronger policies, but on enforceable controls, executive accountability, cross-functional engagement, and cultural alignment. Without these elements, even well-intentioned reforms risk becoming temporary fixes rather than lasting improvements.
Data Governance Failure is rarely visible until disaster strikes. But it is almost always the first domino to fall. Security tools can only protect what governance defines, classifies, and controls.
If your organization has experienced a breach, the question is not just “How did attackers get in?” It’s “Where did governance break down?”
Now is the moment to rebuild with clarity, accountability, and structure.
Don’t wait for another incident to expose deeper weaknesses. Strengthen your governance framework today, align it with risk strategy, and transform your data from a liability into a protected strategic asset.
Because when governance leads, security follows.





6 Comments. Leave new
https://shorturl.fm/AZyiQ
https://shorturl.fm/jctO5
https://shorturl.fm/iL2Q2
https://shorturl.fm/Olf4K
https://shorturl.fm/Eig0x
https://shorturl.fm/0imNq